Automatic speaker verification systems and spoof detection techniques: review and analysis | SpringerLink

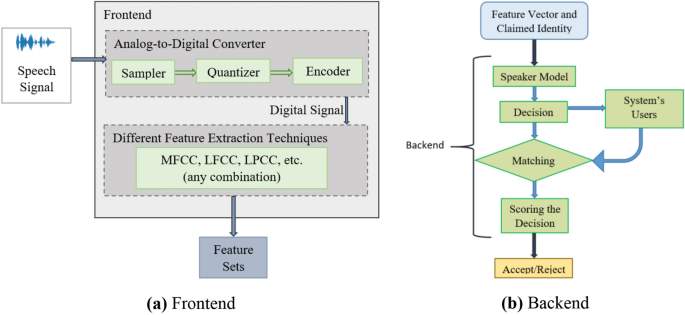
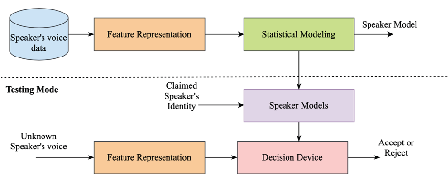
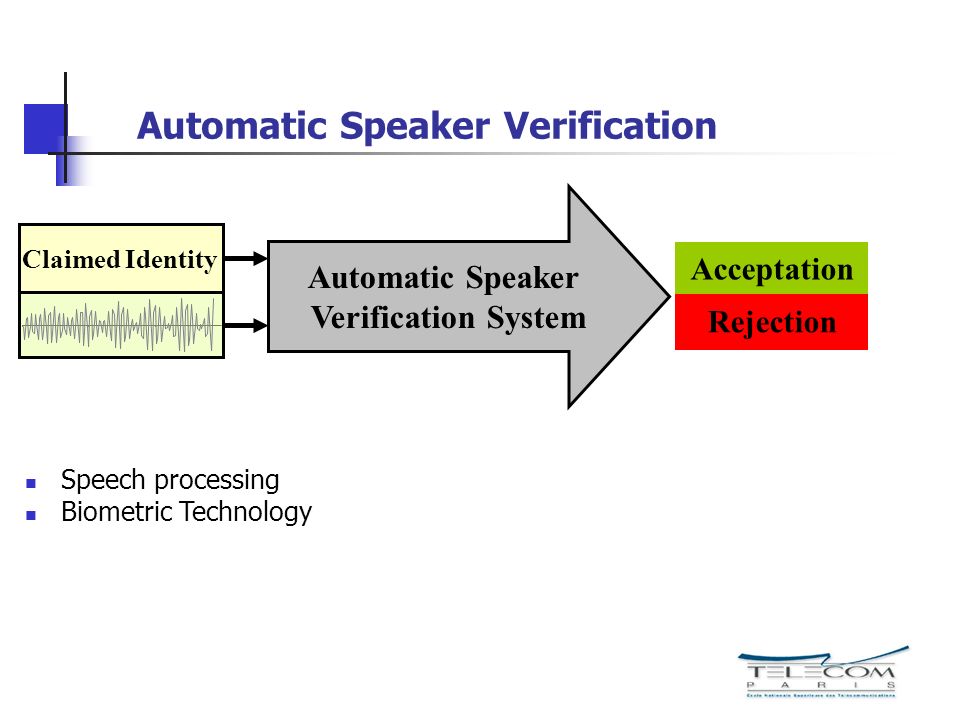
Sensors | Free Full-Text | Automatic Speaker Recognition System Based on Gaussian Mixture Models, Cepstral Analysis, and Genetic Selection of Distinctive Features
![PDF] Black-box Attacks on Automatic Speaker Verification using Feedback-controlled Voice Conversion | Semantic Scholar PDF] Black-box Attacks on Automatic Speaker Verification using Feedback-controlled Voice Conversion | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/15528a632cef3d49d56b98e2f2e39f5393ba1f4e/3-Figure1-1.png)
PDF] Black-box Attacks on Automatic Speaker Verification using Feedback-controlled Voice Conversion | Semantic Scholar
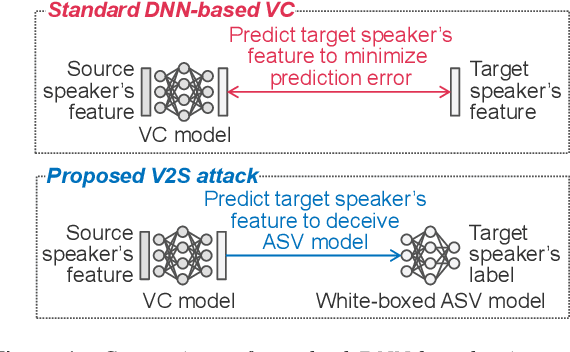
V2S attack: building DNN-based voice conversion from automatic speaker verification: Paper and Code - CatalyzeX

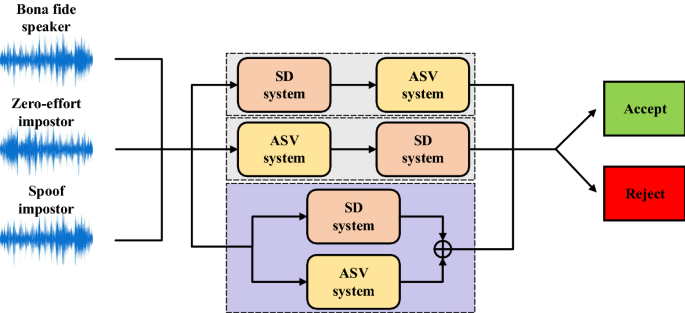
Automatic speaker verification systems and spoof detection techniques: review and analysis | SpringerLink
![PDF] Privacy-preserving sound to degrade automatic speaker verification performance | Semantic Scholar PDF] Privacy-preserving sound to degrade automatic speaker verification performance | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d86a11afcdd9b752e1737ddc1e2a5f03931dab0e/3-Figure1-1.png)
PDF] Privacy-preserving sound to degrade automatic speaker verification performance | Semantic Scholar

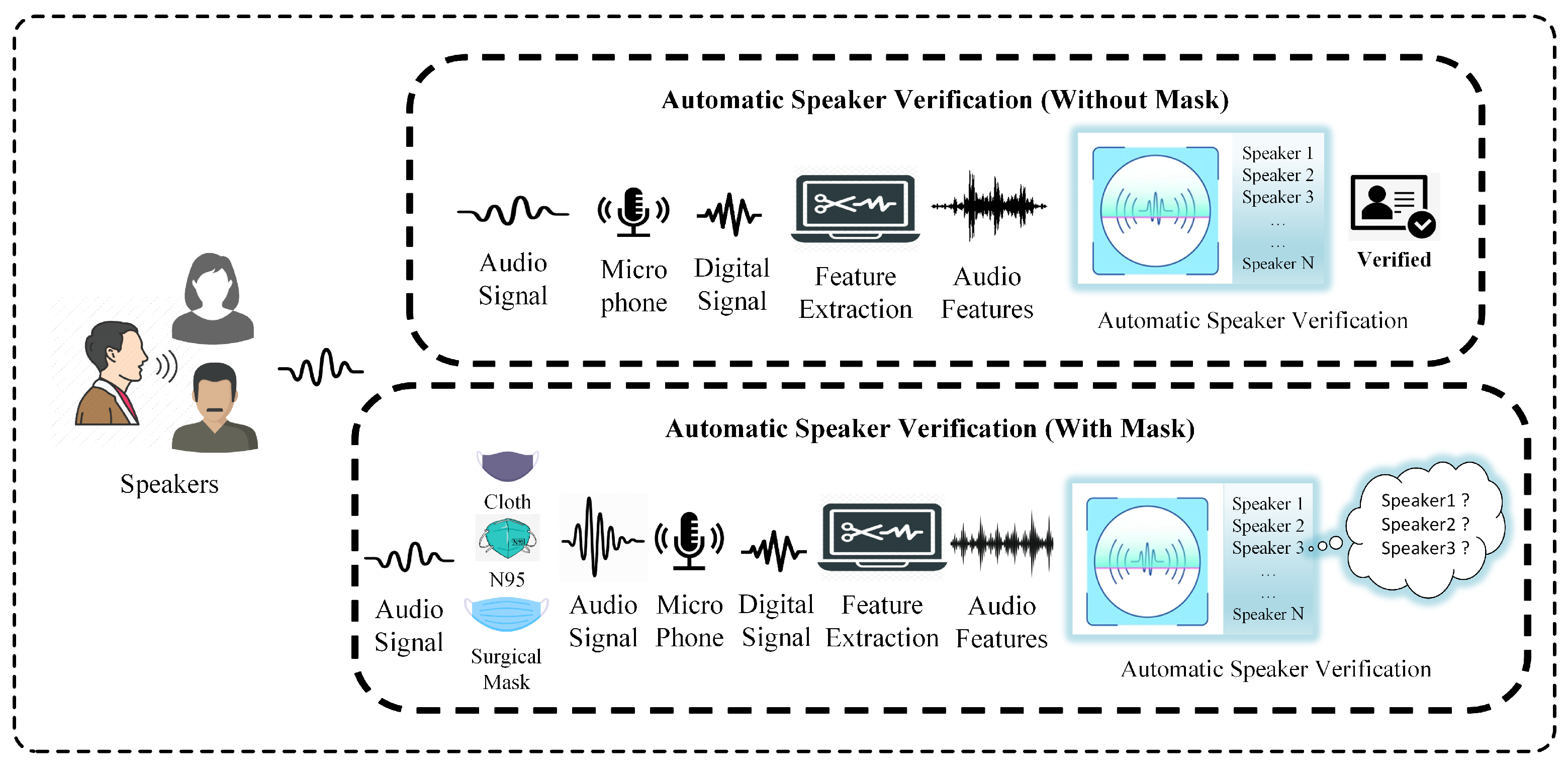
![PDF] Automatic Speaker Recognition: Current Approaches and Future Trends •1 | Semantic Scholar PDF] Automatic Speaker Recognition: Current Approaches and Future Trends •1 | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/51be25a27c5de05818d853eb4ff11b66696c9758/2-Figure1-1.png)






![PDF] The Attacker's Perspective on Automatic Speaker Verification: An Overview | Semantic Scholar PDF] The Attacker's Perspective on Automatic Speaker Verification: An Overview | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/65aa777638c63a81eeec1288f56311b97d6f06bd/1-Figure1-1.png)

![PDF] An overview of automatic speaker recognition technology | Semantic Scholar PDF] An overview of automatic speaker recognition technology | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/691ec89cb048ffe78b6e1eaccb0df7abbd44076d/2-FigureI-1.png)
